AWS SFTP Vs SFTP Gateway - a Comparison
AWS Transfer for SFTP (or AWS SFTP, for short) is a fully-managed service that transfers files into and out of Amazon S3 via SFTP.
While this product is similar to SFTP Gateway, there are certainly some important differences in how each product works, the features they have, and how much they cost.
Here's a quick summary of the differences so you can determine which is the right fit for you. For a full, in-depth comparison, check out this article on our blog.
Feature comparisons
Access to S3 and S3 event behaviors
AWS SFTP provides access to specific S3 buckets and prefixes per user, who can then use SFTP to upload, download, and delete files to and from these buckets.
By default, SFTP Gateway provides an uploads folder and downloads folder for each user. When a file is finished uploading, it is moved to S3 and deleted from the server. The downloads folder syncs its contents from a specified S3 location to provide access to files for a user. The user does not have direct access to S3, but SFTP Gateway can be configured to provide more or less access to users.
AWS SFTP directly uploads files to the S3 location. For SFTP clients that support partial file uploads, such as WinSCP and Filezilla, the S3 location will contain filepart files that will fire S3 events. You will then need to handle these in the S3 event listener.
On the other hand, SFTP Gateway uploads files to the S3 location only when they are finished uploading to the server. It does not transfer filepart files, thus making it easier to know when files are complete and available via S3 events.
AWS SFTP uses MD5 hashes to verify that the files on the server make it to S3 completely, but does not verify that the file made it from the user’s machine to the server. SFTP Gateway allows MD5 verification that allows a user to upload an MD5 sum of the file first to ensure the entire file makes it all the way from their machine to S3.
User authentication methods
AWS SFTP supports common user authentication systems, including MS Active Directory, LDAP, or user authentication within the service. However, this authentication needs to be setup using custom development and API Gateway endpoints.
SFTP Gateway uses a clustered directory service named 389 built into the SFTP Gateway servers. It can be configured to use an external LDAP directory service.
Both allow authentication with SSH keys.
With AWS SFTP, you can use up to 10 SSH keys per user and rotate keys, but you cannot import existing host keys.
SFTP Gateway allows an unlimited number of SSH keys per user with APIs to rotate and change keys. And importing of existing host keys is a standard feature.
SFTP Gateway allows you to use password authentication. With AWS SFTP, password authentication is not provided within the service, but can be supported using an alternative identity provider.
High availability and autoscaling
AWS SFTP provides full redundancy across multiple Availability Zones within an AWS Region. SFTP Gateway provides HA using a network load balancer and autoscaling group.
AWS SFTP uses elastic resources to auto-scale based on workload. SFTP Gateway uses autoscaling to ensure high availability by default. The autoscaling group can be configured using standard AWS techniques to monitor and respond to CloudWatch metrics to scale up and down.
User interface
AWS SFTP has web, API, and CLI interfaces that let you configure your SFTP endpoint and set up client access. It also supports FTP clients like WinSCP and FileZilla.
SFTP Gateway also has web, API, and CLI interfaces to configure your instance and create and edit users. It also supports FTP clients like WinSCP and FileZilla.
Server endpoint access
AWS SFTP provides a way to map domains using Route 53 and other DNS providers. It also allows specifying domain names and custom authentication via API Gateway endpoints.
But AWS SFTP endpoints do not have a static IP address, so it is not possible to create firewall rules that only allow inbound traffic from specific clients or customers. Similarlly, it is not possible for your clients to whitelist traffic to the SFTP server.
SFTP Gateway can be configured to use custom domains by pointing an A or CNAME DNS record at the EC2 instance. Since you have root access to SFTP Gateway, the server can be fully customized for your needs, even allowing creation of AMIs of your custom server. The CloudFormation templates can be customized to fit into your existing network.
Security and compliance
AWS SFTP and SFTP Gateway use similar technologies (SSH, S3), so they are alike with respect to security and compliance. Both use CloudWatch for audit logging.
AWS SFTP allows setting custom roles per user to lock down permissions to S3. SFTP Gateway allows setting roles per SFTP Gateway instance, but also has security in place to prevent users from accessing unauthorized S3 data.
Since SFTP Gateway provides access to the EC2 instances and CloudFormation templates, you can configure security groups and subnets that help strengthen your security. AWS SFTP is always globally available and cannot be placed into one of your subnets.
FTP and FTPS
AWS SFTP does not accommodate the use of FTP or FTPS.
SFTP Gateway allows you to enable FTPS using vsftp. Other protocols can be enabled by modifying the EC2 instance.
Pricing
Pricing is another aspect that is very different between the two products. Here's a quick overview of the pricing structures and two use cases.
Pricing overview
$0.30 for each hour the SFTP endpoint is provisioned
$0.04 per GB uploaded and downloaded via SFTP
Standard charges for S3 usage, AWS data transfer rates for data transferred in and out of AWS SFTP, your VPC, and PrivateLink, SFTP domain name lookups using Route53, API Gateway for access to your identity datastores, CloudTrail, and CloudWatch Logs and Events.
$0.06 for each hour the SFTP server is running (this pricing is for SFTP Gateway 2.0)
The cost of the EC2 instance you run
Standard charges for S3 usage, AWS data transfer rates for data transferred in and out of SFTP Gateway, your VPC, and PrivateLink, SFTP domain name lookups using Route53, API Gateway for access to your identity datastores, CloudTrail, and CloudWatch Logs and Events.
Cost examples
Below we quickly go over a couple of cost scenarios for AWS SFTP vs. SFTP Gateway. For a full analysis, check out our comparison blog post.
Example 1: Light Use
Let’s say you have 20 end users who download a total of 1 GB of data per day. Here’s a table that provides a high-level overview of pricing:
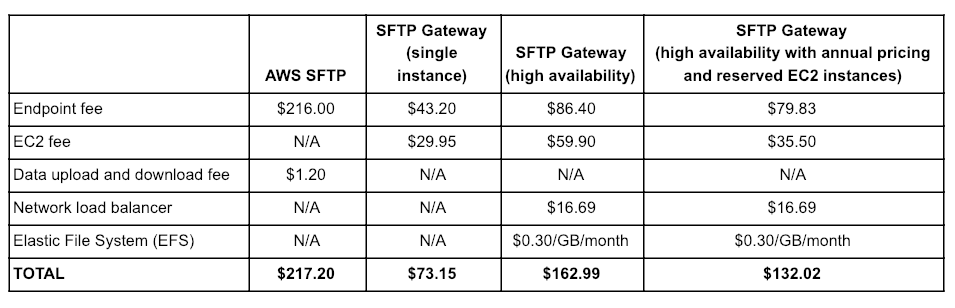
As you can see in the table above, for the light use case, SFTP Gateway is 18-63% cheaper than AWS SFTP.
Example 2: Heavy Use
Now let’s say your organization transfers or receives lots of files via SFTP. You have 1000 end users who upload 100 GB/day and download 50 GB/day. Pricing for each product might look like this:
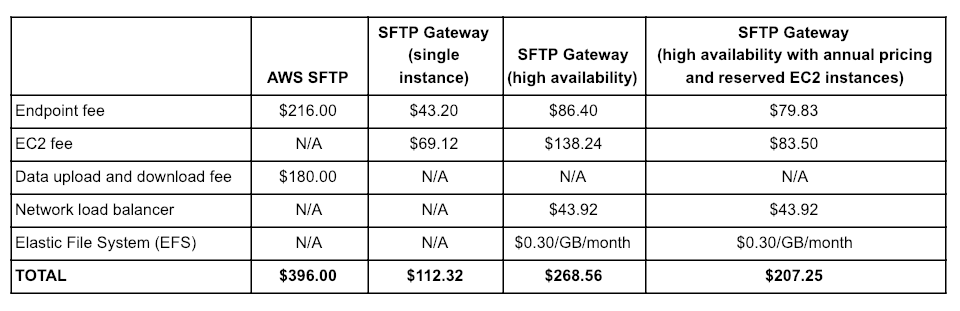
For the heavy use case, SFTP Gateway is 28-70% cheaper than AWS SFTP.
Conclusion
While AWS SFTP and SFTP Gateway are similar products, there certainly are differences where one product may work better for your organization. We hope that this article shed some light on which may be the better fit for you.
If you have any questions, check out our full comparison blog post or email us at support@thorntech.com.