Launching into AWS GovCloud
AWS GovCloud is an account that is attached to a primary organizational account. Currently SFTP Gateway can only be launched into the US-Gov-West region of the AWS GovCloud.
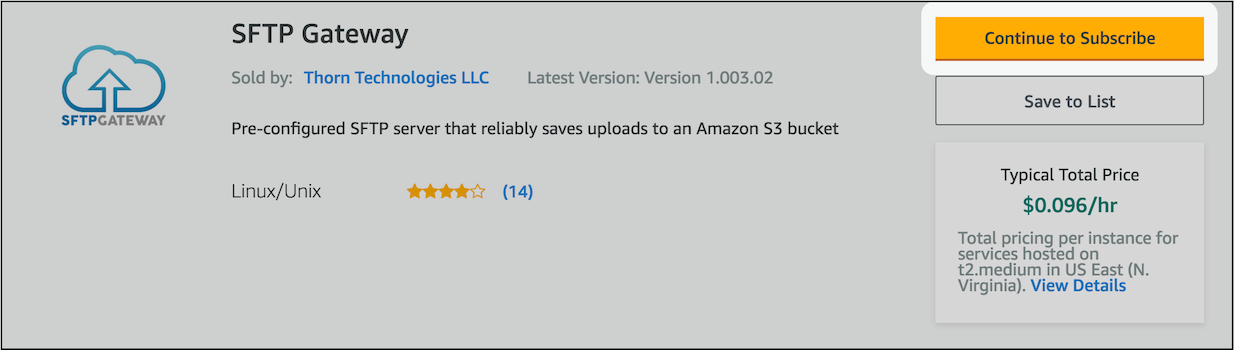
Subscribing to SFTP Gateway
In order to launch SFTP Gateway into the AWS GovCloud, your root organizational account must be subscribed to SFTP Gateway.
To do this:
Login to your root organizational account
Go to the AWS Marketplace page for SFTP Gateway
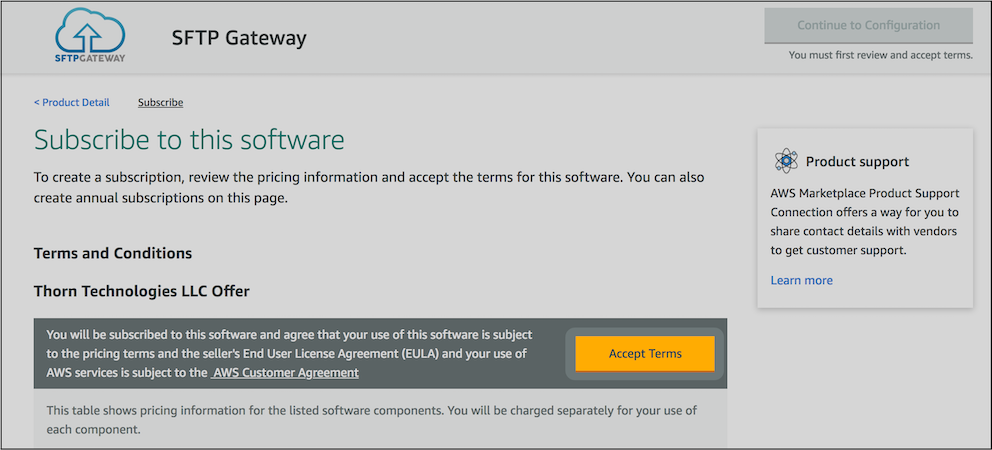
Click the Continue to Subscribe button
Click the Accept Terms button.
AWS GovCloud currently does not allow you to launch directly from the AWS Marketplace. You can launch SFTP Gateway into the AWS GovCloud with either the EC2 console launcher, or with the SFTP Gateway CloudFormation template.
Launching through CloudFormation
To launch SFTP Gateway with the CloudFormation template, download the latest CloudFormation template
- SFTP Gateway Classic template
- SFTP Gateway 2.0 single instance template
- SFTP Gateway 2.0 HA template
- SFTP Gateway 2.0 HA existing network template
Then, follow the instructions outlined in the CloudFormation Setup section of our Initial Setup knowledge base article.
Launching from the EC2 Console
Before you begin
There are a couple items that you will need in order to configure an SFTP Gateway instance.
You will need an SSH key pair stored in your AWS GovCloud account. If you do not have one already, you can create one by going to the EC2 console -> Key Pairs -> Create Key Pair. Give you key pair a name and click Create, then your browser will download the private key portion of the key pair. Keep this private key in a secure location. It will be needed if you need to connect to your instance over SSH.
You will also need an IAM Role that will allow your EC2 instance to access S3. For more information see the Create IAM Role section of our Initial Setup knowledge base article.
Launching the instance
To launch directly from the EC2 console:
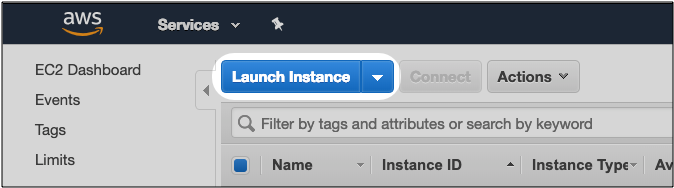
Login to the EC2 console
Click Launch Instance
Click on the AWS Marketplace tab. Enter SFTP Gateway in the search box and select the SFTP Gateway AMI
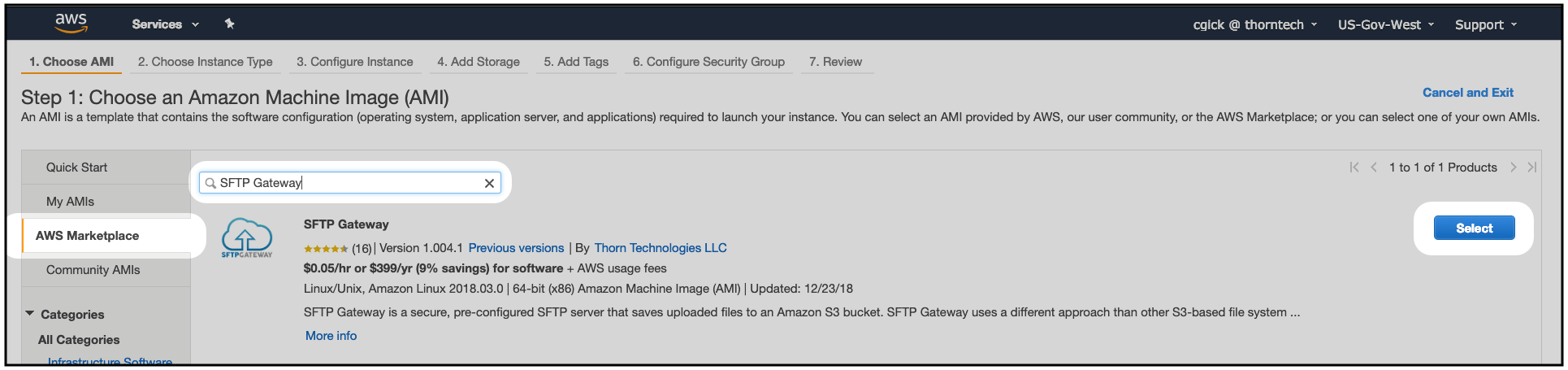
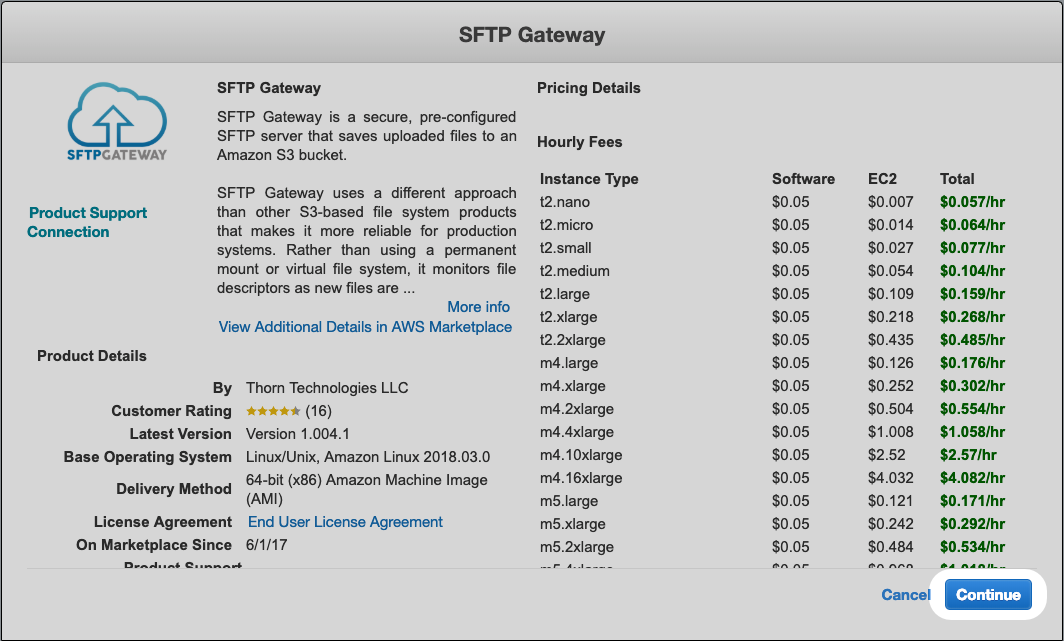
The popup will outline the SFTP Gateway pricing. Click Continue
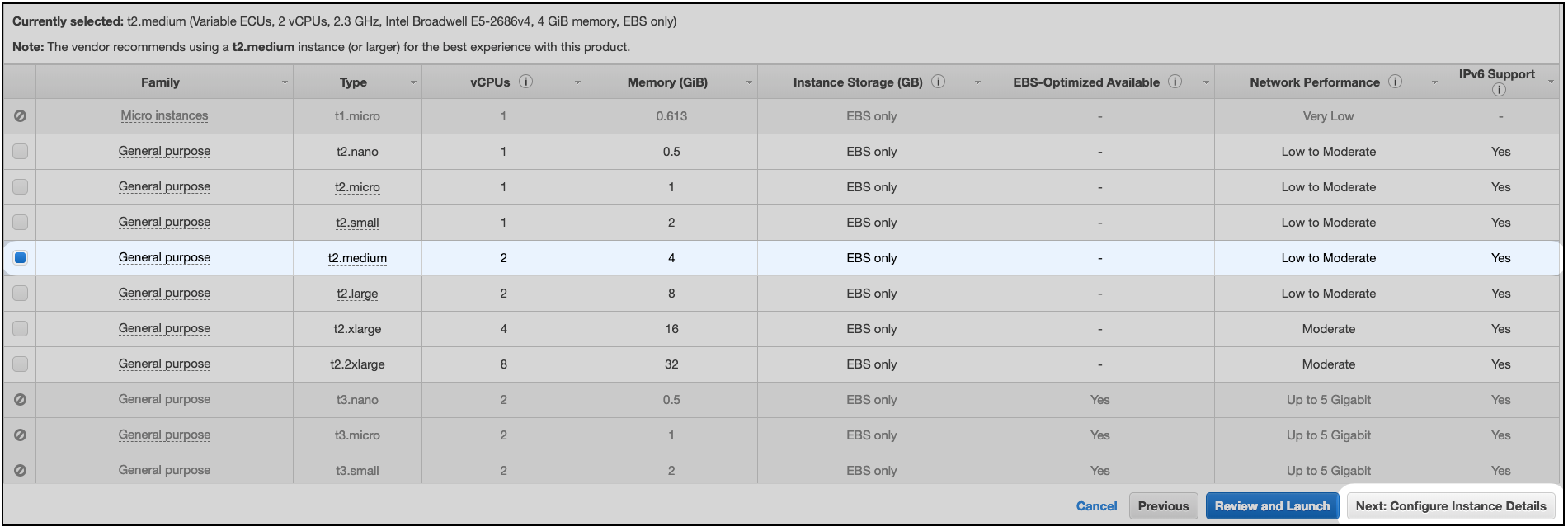
Select the EC2 instance type you wish to deploy on, and click Next: Configure Instance Details
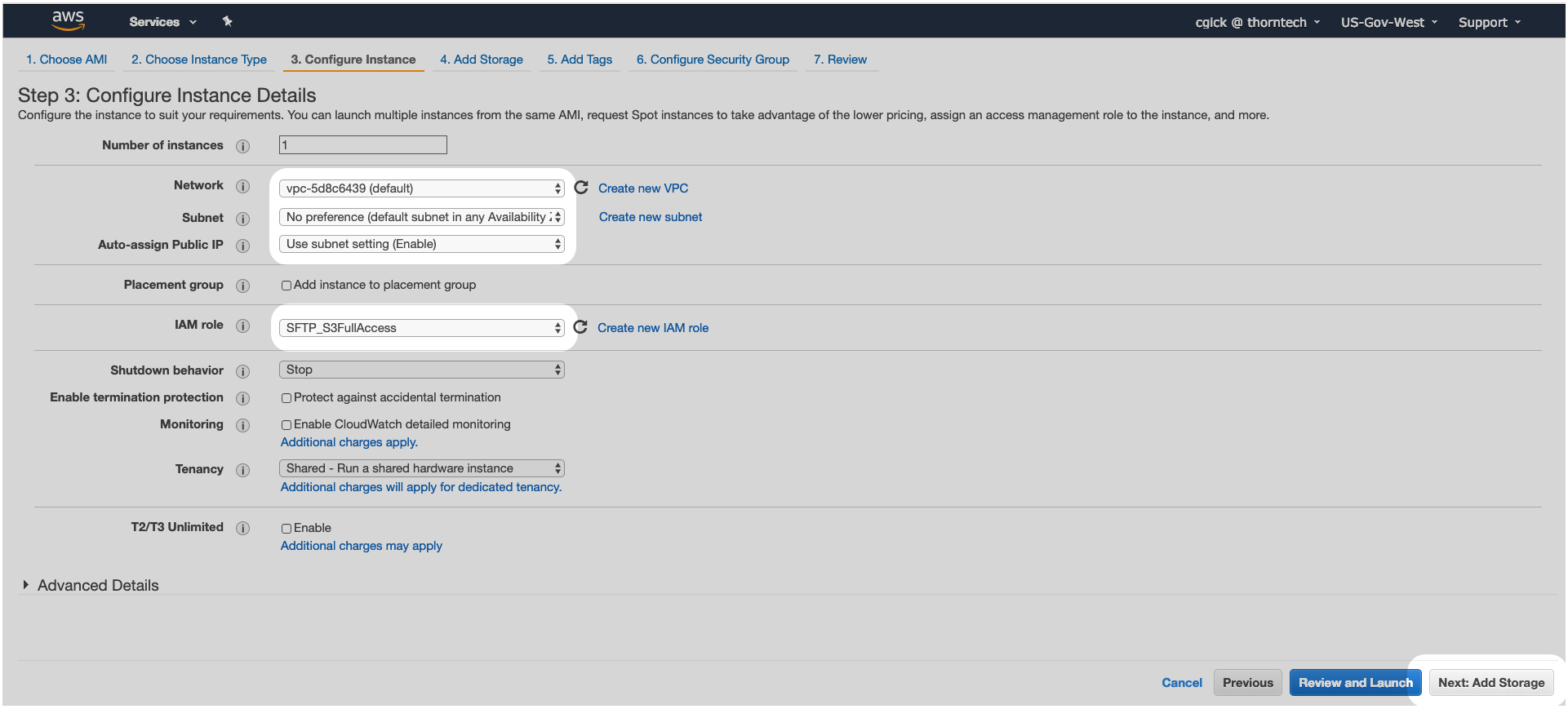
On the Instance Details page select the following and click Next: Add Storage;
- The desired VPC
- The desired Subnet
- The IAM Role that was created earlier to allow EC2 to access S3
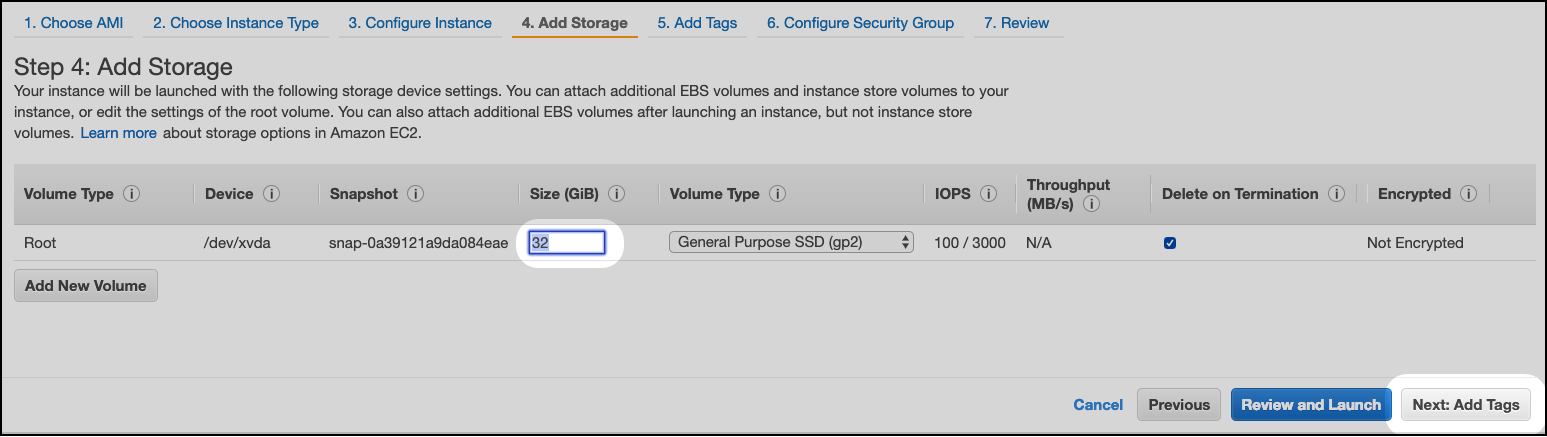
Enter a Size in GB that will allow you to buffer uploaded files as they are transferred to S3 (this must be a minimum of 32 GB), and click Next: Add Tags
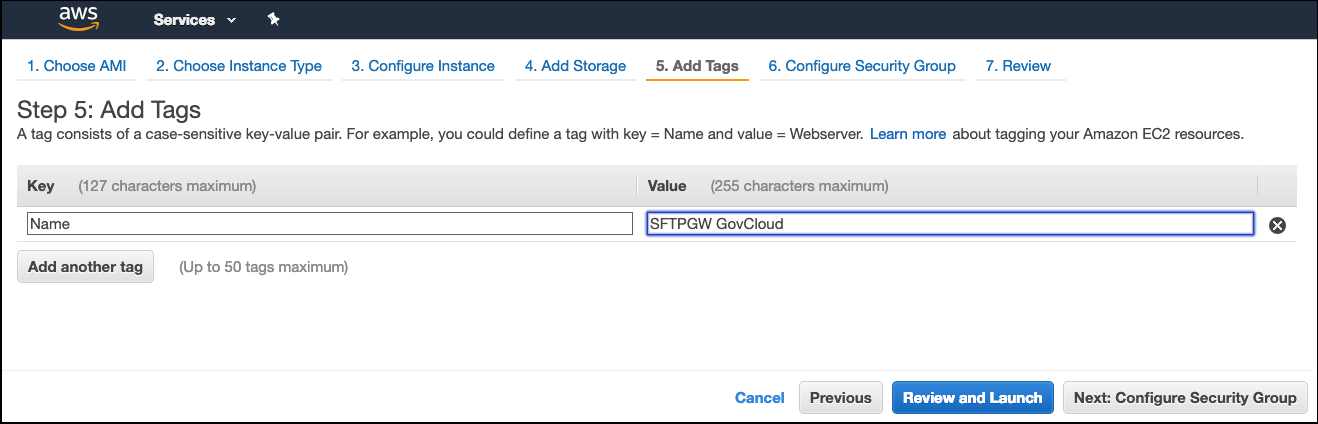
(Optional) Enter a tag that will allow you to identify your SFTP Gateway instance, and click Next: Configure Security Group
Enter the IP range of traffic that you would like to allow to your instance and click Review and Launch
Note: Security Groups control IP traffic to your instance based on Port number. Port 22 is used for SSH access to your instance, and by extension SFTP access as SFTP is a subset of the SSH protocol. If left at
0.0.0.0/0port 22 will be open to the world. You can create a whitelist of allowable IP traffic to your instance by entering public IP ranges in the Source field. To check your own public IP address you can go to http://checkip.dyndns.org/ then convert it to a range by adding/32at the end of the address. Security groups can be changed at any time. For more information see our knowledge base article Configure an EC2 security group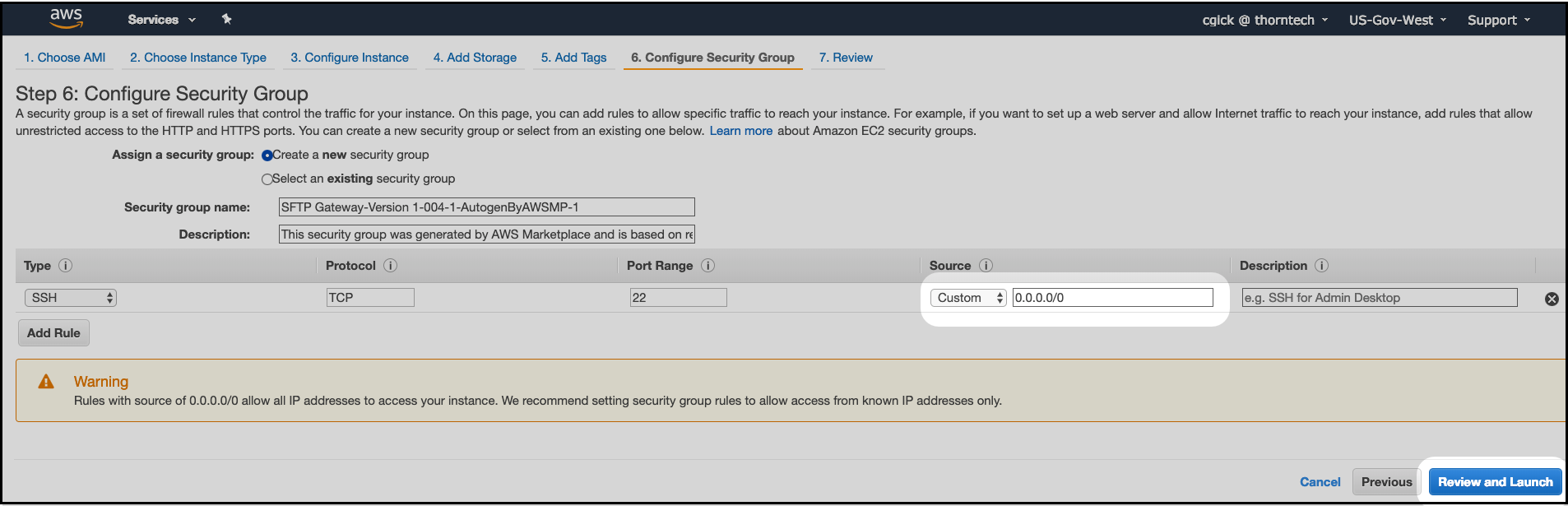
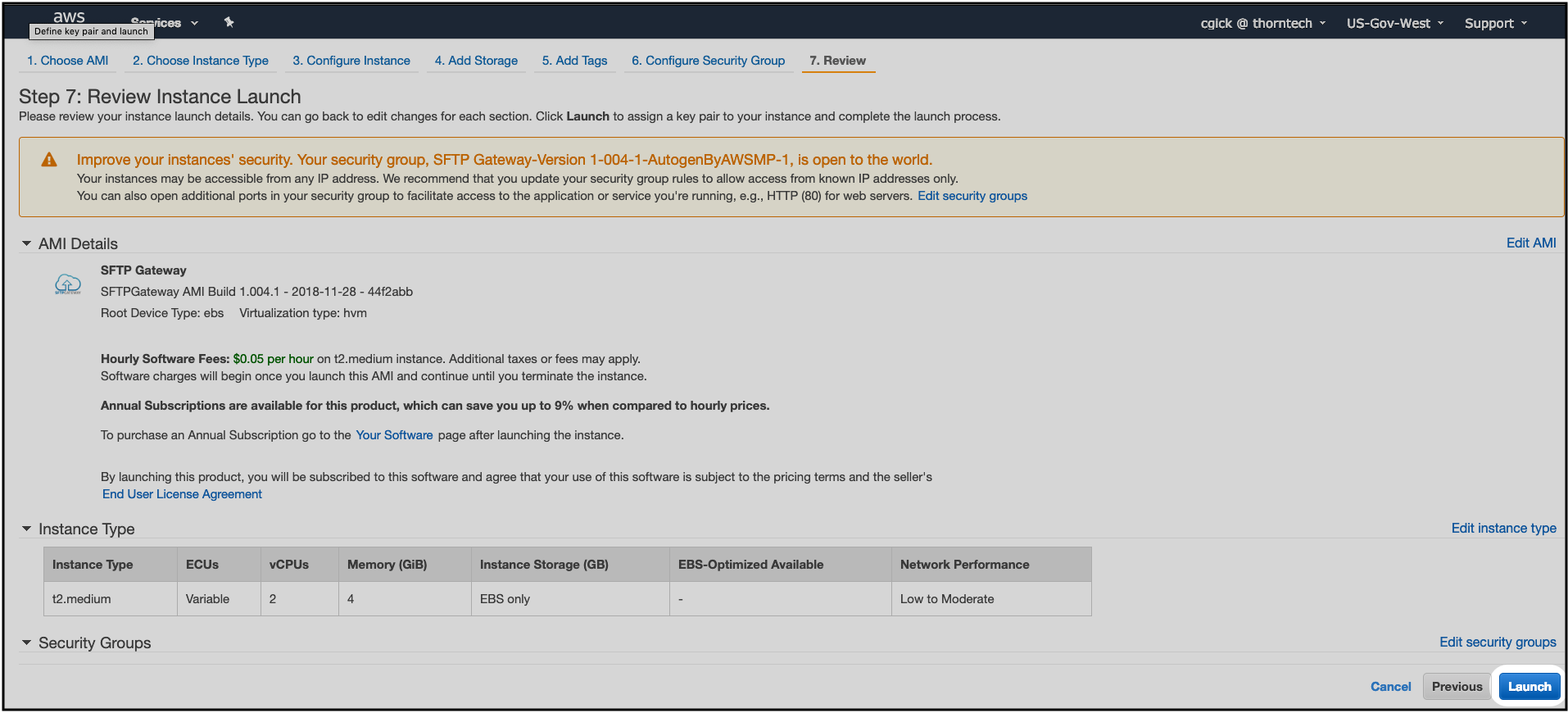
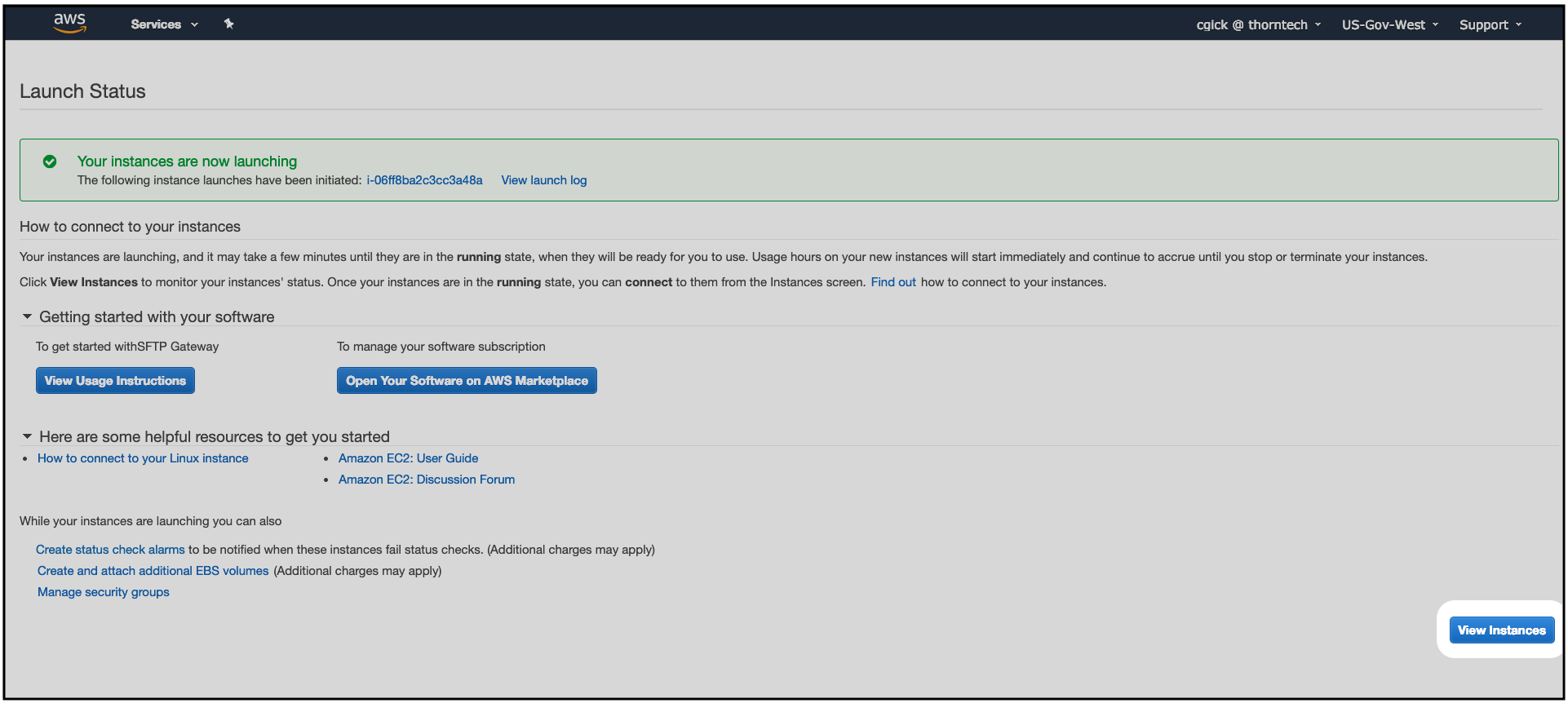
Review your EC2 instance configuration and click Launch
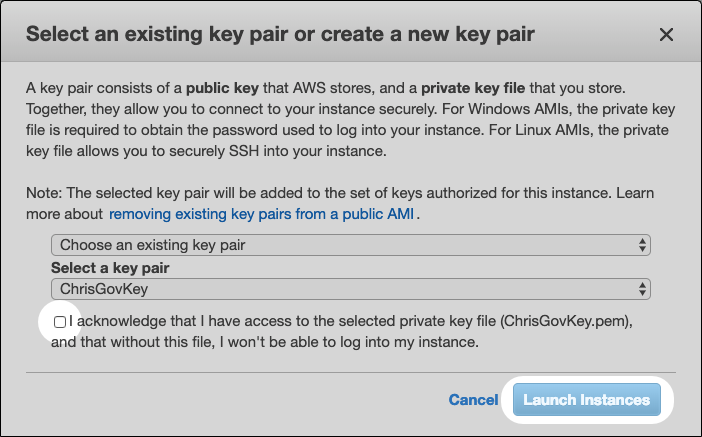
You will be prompted to select an SSH key pair. If you have a key pair already stored in you account you can select it from the list and check the box acknowledging that this is indeed your key pair and you have access to it, and click Launch Instances
Click View Instances to return to the EC2 console.
Where to go from here
Now that you have an SFTP Gateway server in the AWS GovCloud, the next step is to setup users. Refer to our Add and configure usersknowledge base article for instructions.
Check out our reference article for SFTP Gateway commands, user and server properties, sftp commands for users, troubleshooting items, and log locations.