Launch a Virtual Machine
Note: This page applies to SFTP Gateway version 2.x. Visit Here for documentation on version 3.x.
Overview
You can launch SFTP Gateway as a virtual machine from the Azure Marketplace. For the most part, you can accept the defaults when going through the wizard. But as with any VM, you do need to configure some advanced settings on the Networking tab. This is because you want to limit SSH and web access to your own IP address.
Launch SFTP Gateway from the Azure Marketplace
Visit the SFTP Gateway page on the Azure Marketplace.
Click the Get it Now button to the left.
You should see a Create this app in Azure modal.
You may be prompted to supply some profile information.
Otherwise, click Continue.
You will be redirected to a product landing page on the Azure portal. Click Create.
You will be redirected to the Create a virtual machine wizard.
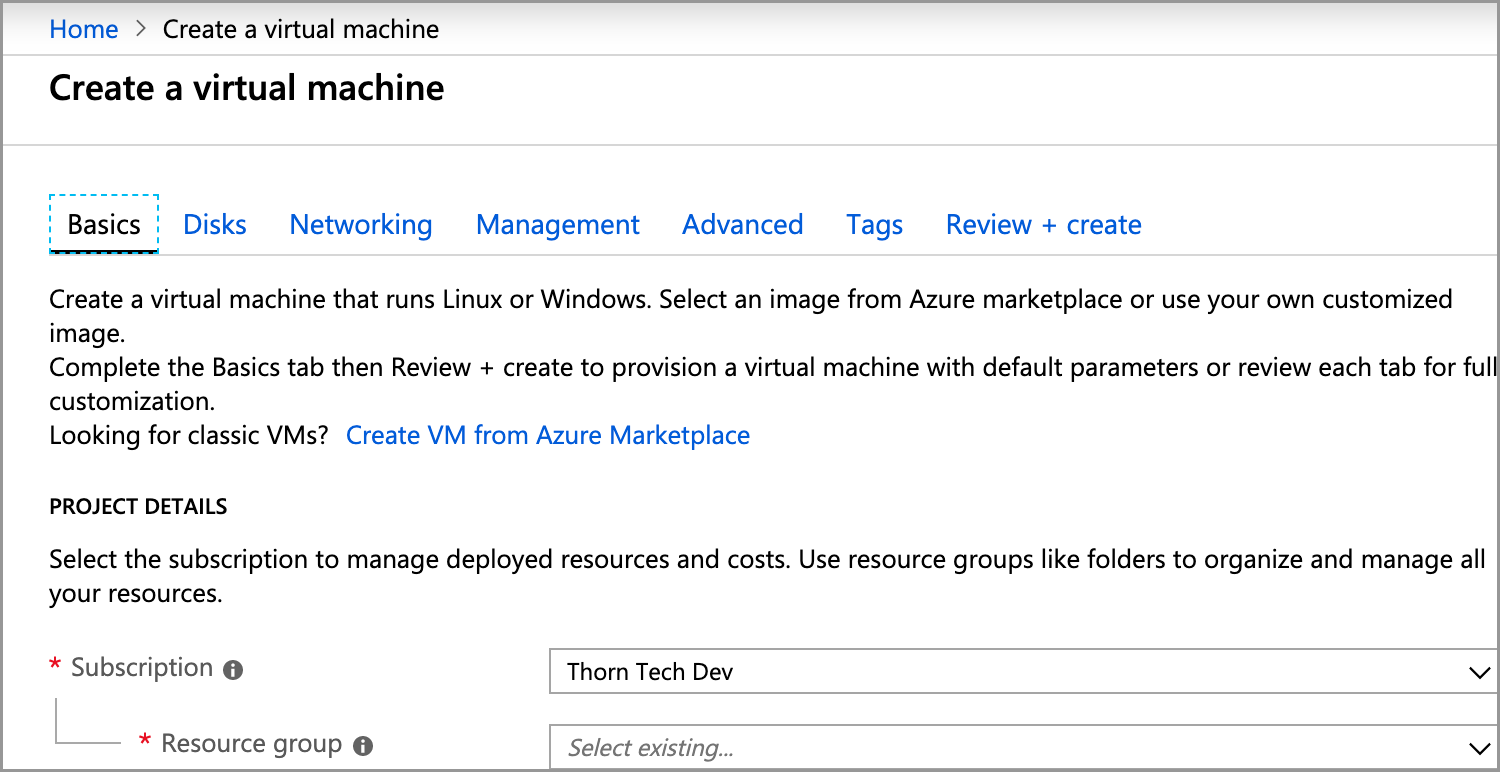
Go through the Create a virtual machine wizard
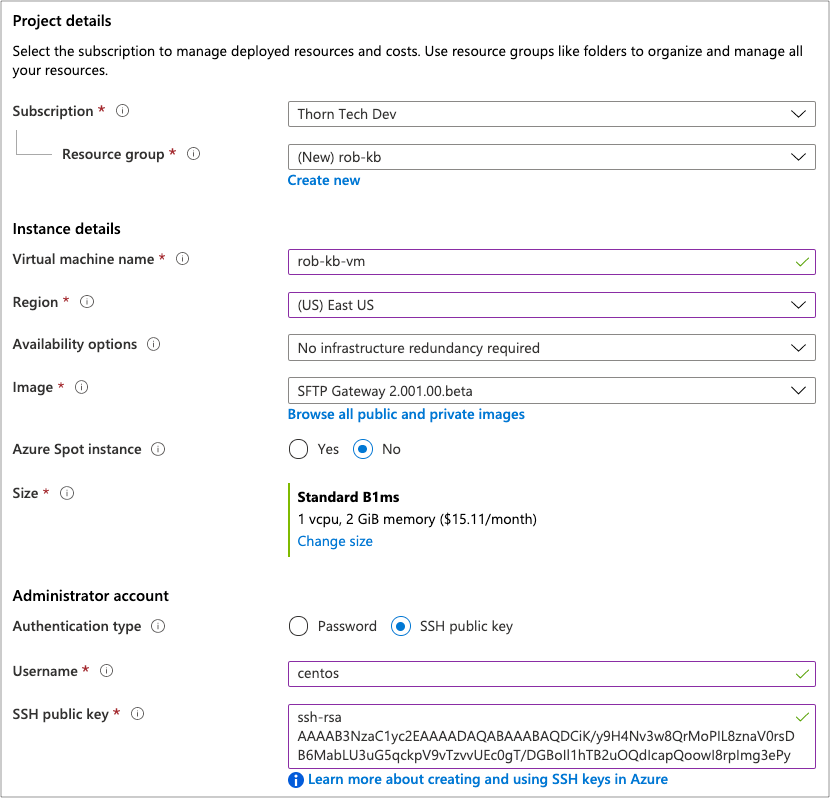
On the Basics tab, fill out the following information:
- Resource Group: Click Create New and enter a name. Or, select an existing one from the drop-down menu.
- Virtual machine name: Enter a name for your VM.
- Size: For testing purposes, you can use B1ms. For production, we recommend one of the D sizes.
- Authentication type: Select SSH public key authentication.
- Username: Enter a username, such as centos.
- SSH public key: Paste in a public key in which you have access to the private key. See this article to create a key pair using PuTTY.
- Public inbound ports: Keep this at the default None. You will later configure advanced options on the Networking tab.
The form looks like this:
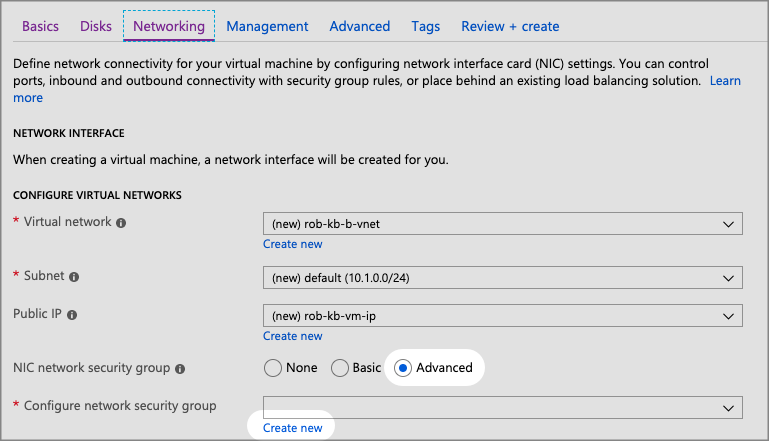
Click on the Networking tab, and configure the following options:
- Virtual network, Subnet, Public IP: These should auto-populate based on information you provided earlier.
- NIC network security: Select Advanced
- Configure network security group: Click Create new
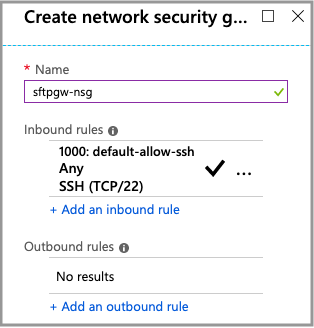
Configure inbound rules on the network security group.
This is where you grant your IP address access to ports 22, 80, and 443.
In the Create network security group window to the right, click on the existing Inbound rule 1000: default-allow-ssh.
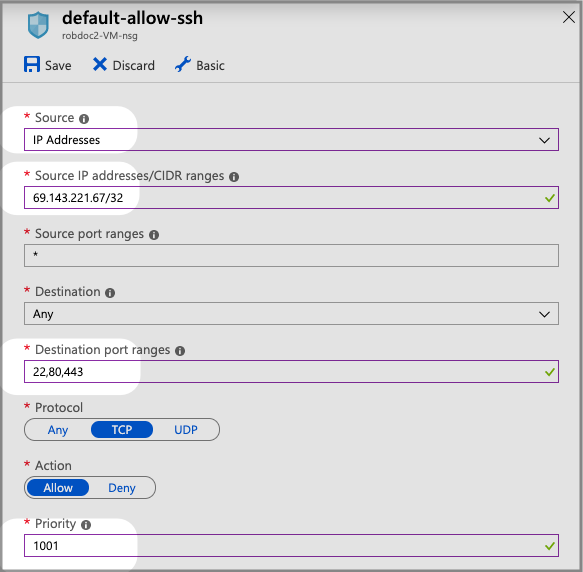
Then edit the following fields:
- Source: Change this from Any to IP Addresses
- Source IP addresses/CIDR ranges: Paste in your IP address, followed by /32 to specify a range of a single IP. Note: You can get your current IP address from http://checkip.dyndns.org
- Destination port ranges: Change this from "22" to "22,80,443"
- Priority: Change this to 1001. Otherwise it won't save.
Click Save
Click OK at the bottom to close the Create network security group window.
Click the Review + create tab on the top
It will take a few moments to validate. You should see "Validation passed" in green. Otherwise, go back and address any issues.
Review your information and click Create on the bottom.
It will take a few minutes to provision your VM.
Once complete, you should see your Resource Group with the following resources:
- Virtual machine: This is the SFTP Gateway server.
- Public IP address: When you stop the VM, you will be given the option to reserve the IP address. Make sure you do so.
- Storage account: This contains diagnostic information for your VM.
- Network security group: This acts as a firewall for the VM.
Where to go from here
Next, proceed to the Initial Configuration page to SSH into the VM and perform a one-time setup.