Configure System Settings Using UI
Overview
This document covers the Settings page in the admin web UI.
On the Settings page, you can:
- Manage admin web users
- Configure Cloud connections (these define an S3 bucket destination, and related settings)
- Backup and Recovery
You can navigate to it by clicking on Settings in the top nav menu.
Admin Users
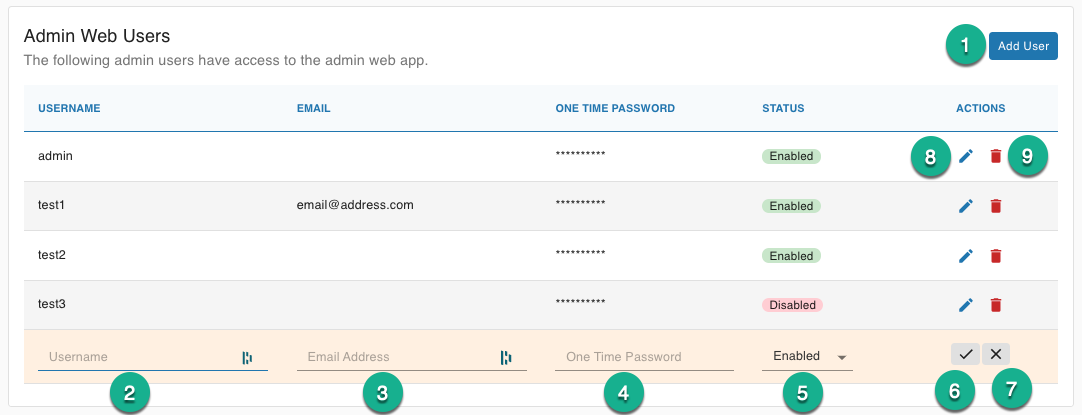
The admin users can log into the admin web interface and manage users connections and folders.
Add User will open a new editable row in the Admin user table.
Username Required username must be unique among admin users.
Email Address (Optional) email address associated with the admin user.
One Time Password sets a temporary password for the admin user, and they will be forced to reset the password when they log into the web ui for the first time. Can also be used to reset an admin's password.
Status allows you to enable or disable the admin use. Disabled user will not be allowed to login to the admin web ui.
Confirm saves the admin user.
Cancel will close the row without saving.
Edit User will allow make the table row editable to update an admin user.
Delete User removes the admin user.
Cloud Connections
A Cloud Connection defines a S3 Bucket destination, and its related settings.
Here is an example of a Cloud Connection:
- S3 Bucket:
s3://rob-test-bucket - S3 Encryption Option:
SSE-S3 - Cloud Connection Credentials: Uses the instance profile credentials
Once a Cloud Connection is defined, you can start creating Folders (every folder must point to a Cloud Connection).
You can point multiple Folders to a single Cloud Connection. This way, the Cloud Connection becomes a single point of change (e.g. you need to rotate an AWS Access key).
Click on Create AWS Connection, and you will see this page:
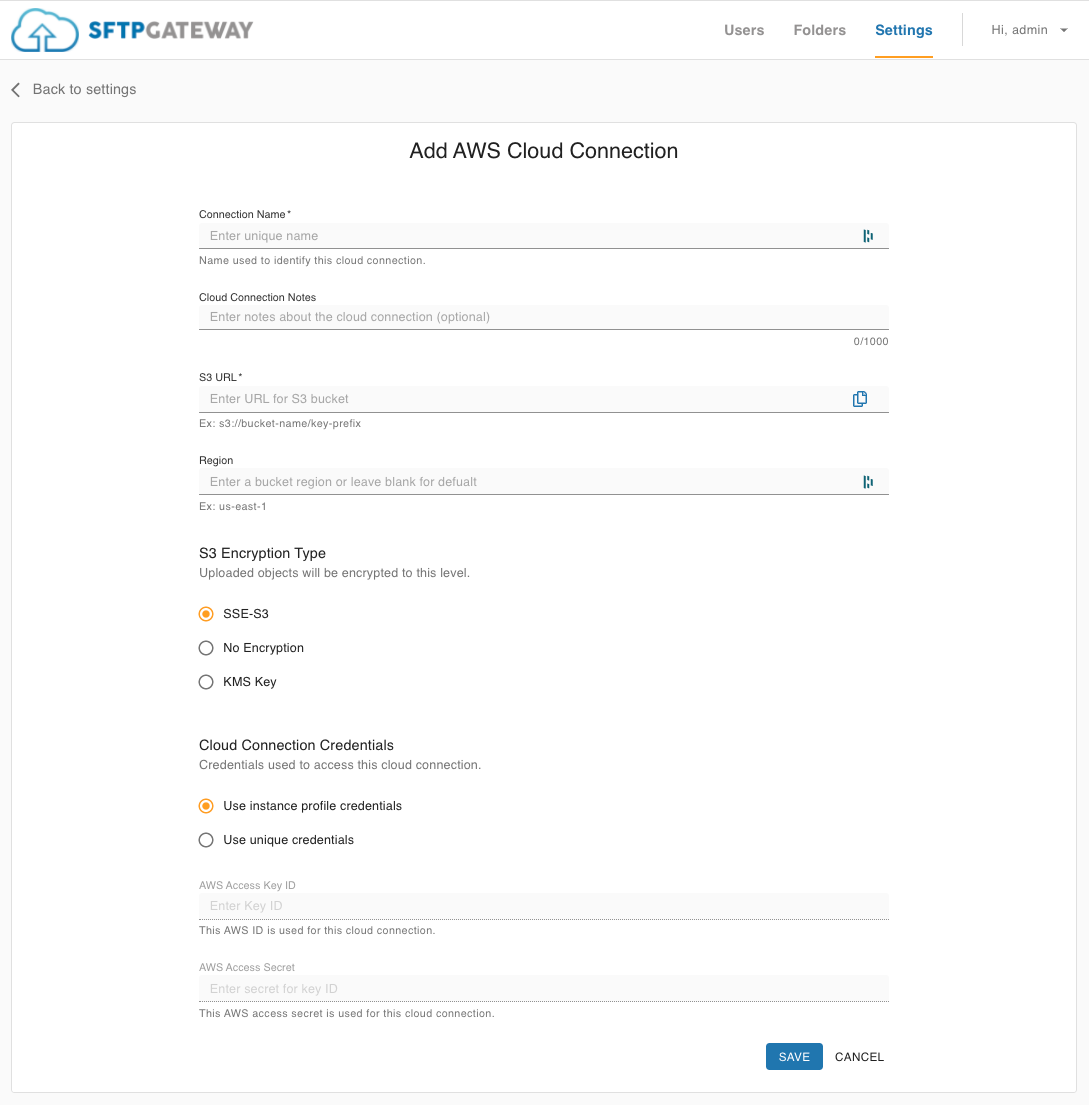
Fill out the following fields:
Connection Name:
A name you define in order to refer to this Cloud Connection.
Cloud Connection Notes:
Optional field for providing more context about this Cloud Connection.
S3 URL:
Enter the S3 Bucket name. Remember to follow the standard S3 Bucket naming convention:
- Has to be globally unique (cannot conflict with S3 buckets in other AWS accounts)
- Lowercase letters (no uppercase allowed), numbers, and hyphens
- Must have fewer than 63 characters
- Only include the S3 bucket (i.e. don't include the folder path)
Region:
The AWS region in which the S3 Bucket is located. If left blank the region of the SFTP Gateway server will be used.
S3 Encryption Option:
S3 objects are encrypted at the time of upload. The encryption method you define on the Cloud Connection will apply to all subsequently uploaded S3 objects.
- SSE-S3: The S3 service manages encryption behind the scenes. S3 objects are encrypted at rest, and the S3 service automatically decrypts the object so long as you have read-access.
- KMS: KMS encryption offers more security value, because KMS key permissions are decoupled from S3 access permissions.
- No Encryption: Do not override encryption settings, so that objects are encrypted using the S3 bucket's default encryption setting.
Cloud Connection Credentials:
The Use instance profile credentials option leverages the IAM permissions on the EC2 instance. This is the recommended approach, because the access key credentials are handled transparently, and rotated for you automatically.
If you want to restrict S3 permissions on a per-user basis, select the Use unique credentials option. You can set AWS Access Key credentials on the Cloud Connection. And then each SFTP can have their own dedicated Cloud Connection.
Backup & Recovery
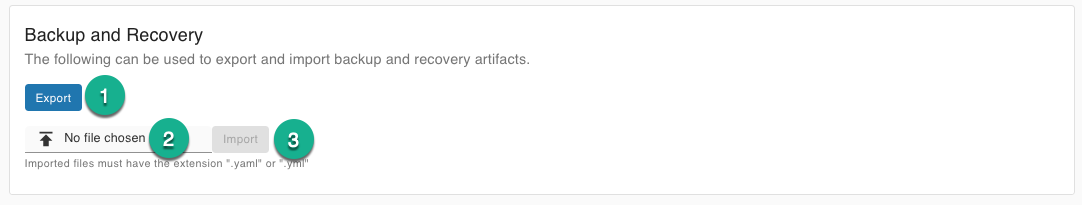
The backup and recovery section and be used to export/import the SFTP users, admin user, folders, and cloud connections of your SFTP Gateway server in a flat YAML backup file. This backup file can that be used to restore your server in the event of failure or migration to a new server.
Export will download all of your users, folders, and cloud connections into a yaml file with the name
sftpgw-backup-<date-time>.yamlFile Selector allows you to browse your file system for a specific backup file.
Import will import the file and then display a number of status messages related to the imported items.