Creating a High Availability deployment on Google Cloud
Overview
You can launch an HA configuration of SFTP Gateway Professional using a yaml configuration file. High-availability requires additional resource types like a database, load balancer, and autoscaler. The Google Deployment Manager coordinates the provisioning of these resources.
These instructions are for provisioning SFTP Gateway Professional version 3.7.1.
Prerequisites:
- Enable Cloud Storage Admin Api
- Enable Cloud Resource Manager Api
- Create a Peered Service Network for the default VPC by following the steps at: https://cloud.google.com/database-migration/docs/mysql/configure-connectivity-vpc-peering#configure-access
- Grant the
Google APIs Service Agentthe Editor & Security Admin roles.
Navigating to the command line interface
In the Google Cloud Console, you should see the Cloud Shell icon at the top of your screen, to the right of the search bar. Click this to open up the command line console.
Deployment Procedure
- Create a yaml configuration file (config.yaml) with the command:
touch config.yaml
- Then use your favorite command line text editor to edit the file:
nano config.yaml
- Paste this into the config.yaml file and change the first (64.98.240.105/32) adminSourceRanges property to your own IP address. Keep the 35.235.240.0/20 IP address as this is a Google address and allows you to SSH via the Google console. You only need to configure the properties since we're referencing a script to create the resources such as the database and load balancer for example.
resources:
- name: solution
type: gs://sftpgateway-public-scripts/deploy/v3.7.1/solution.jinja
properties:
adminSourceRanges: 64.98.240.105/32, 35.235.240.0/20
isHighlyAvailable: True
The solution uses sensible defaults to configure the architecture. The adminSourceRanges property is required for accessing the admin console and expects a comma-separated list of CIDR addresses from which you'd like to access the admin UI.
Optional properties include:
- isHighlyAvailable (Default: False) If set to True, High Availability will create a managed database service, autoscaler, and load balancer. SFTP Gateway instances are spread to different zones within a region, allowing it to automatically recover if a zone fails. Since we want High Availability you want this set to True.
- adminUsername (Default: admin)
- zone (Default: us-east1-c)
- machineType (Default: e2-medium)
- network (Default: default)
- Run this command to deploy the solution, replacing 'sftpgw-deployment-name' with your desired deployment name:
gcloud deployment-manager deployments create sftpgw-deployment-name --config config.yaml
- Once the deployment has succeeded, run this command to generate the deployments output such as the admin credentials and external ip address. Make sure you're replacing 'sftpgw-deployment-name' with the name you used in the previous command:
gcloud deployment-manager manifests describe --deployment sftpgw-deployment-name --format json | python -c "import sys, json; print(json.load(sys.stdin)['layout'])"
Note: You can also find the outputs by going to the Deployment Manager service and viewing the Layout of your deployment.
- Note the "finalValue" for outputs named
vmExternalIp,adminUsername, andadminPasswordas you will need these to access the SFTP Gateway admin console. For example, the output of the previous step could look like:
resources:
- name: solution
outputs:
- finalValue: sftpgw-deployment-name
name: deployment
value: sftpgw-deployment-name
- finalValue: sftp-gateway
name: project
value: sftp-gateway
- finalValue: 35.243.239.136
name: vmExternalIP
value: $(ref.solution-vm-tmpl.ip)
- finalValue: '942030955628191395'
name: vmId
value: $(ref.sftpgw-deployment-name-vm.id)
- finalValue: 10.142.0.26
name: vmInternalIP
value: $(ref.solution-vm-tmpl.internalIP)
- finalValue: admin
name: adminUsername
value: admin
- finalValue: KyT+xjn1inoo
name: adminPassword
value: $(ref.generated-password-admin.password)
properties:
adminUsername: admin
bootDiskSizeGb: 20
...
In this example you will see that the vmExternalIP is 35.243.239.136, adminUsername is admin, and adminPassword is KyT+xjn1inoo.
Access the SFTP Gateway console
In your browser, navigate to the vmExternalIp. Then use the adminUsername and adminPassword values from your deployment to log into SFTP Gateway.
You now have access to add SFTP Users and do further configuration in the SFTP Gateway admin console.
Access the VM via SSH
In the Google console, go to your VM and under the details tab, go to SSH -> Open in browser window on custom port.
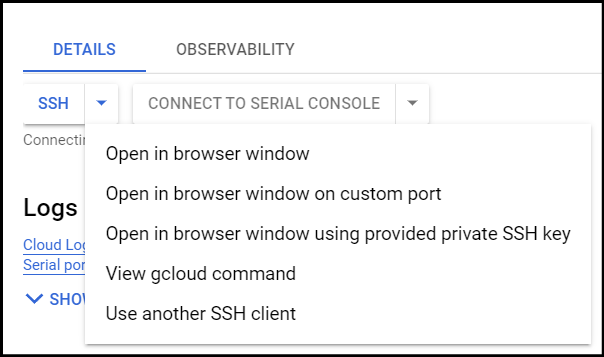
When prompted for the custom port, use port 2222. You should now be connected to the VM.