Backup & Recovery, or Upgrade
Overview
This article outlines a backup and recovery process that you can use for disaster recovery. It's important that you test this scenario yourself, so you know what to expect beforehand.
You can also use this as a migration process to upgrade to the newest version of SFTP Gateway.
Backup
There are a few steps you can perform now to prepare for a server outage or when performing a migration to an upgraded version of SFTP Gateway.
Export your users and settings
Go to the web admin portal for SFTP Gateway.
On the Settings page, click the Export button.
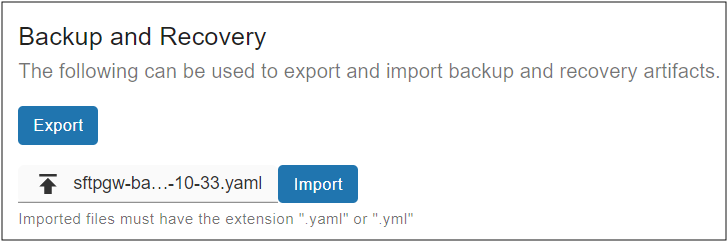
This will download to your local machine a yaml backup artifact containing your SFTP users and settings.
Note: You may want to export this yaml file on a regular basis.
Back up the server host keys
The SFTP Gateway server host keys are located in:
/opt/sftpgw/
There's a public and private key pair for each algorithm. For example:
ssh-rsa
ssh-rsa.pub
Copy these files to the Linux admin home directory, so you can copy them off the server.
Back up SSL certificates
If you installed a commercial SSL certificate, you may want to back up these files which are located here:
/etc/nginx/sites-available/website.conf
Make sure you get the Nginx conf file (e.g. website.conf) as well as the SSL certificate and key that points to.
Restore
Deploy a new instance of SFTP Gateway, and this will used to restore your users and settings.
Then, perform the following steps.
Import your users and settings
Find the yaml backup artifact, and import it into the Settings page.
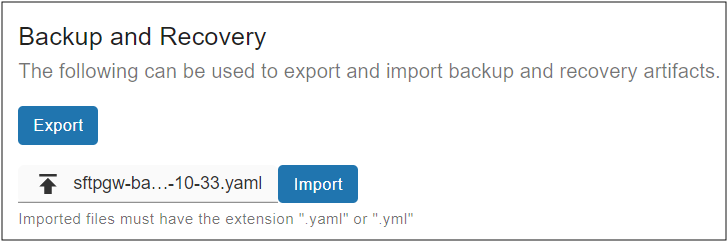
You should see some log output on the screen, as users are imported.
Import the server host keys
If you have the server host keys from the Original VM,
copy them to /opt/sftpgw/ on the Recovery VM.
Note: If there aren't any server host keys, SFTP Gateway attempts to create new ones whenever an SFTP user authenticates. So you may need to delete them.
Import SSL certificate
If you exported a commercial SSL certificate, remember to re-import it.
To apply your Nginx changes, restart the service:
sudo su
nginx -t && service nginx restart